INTELLIGENT AND EMERGING TECHNOLOGIES IN BUSINESS ORGANIZATIONS
Topics Covered:
- Artificial Intelligence
- Cloud Computing
- Blockchain
- Quantum Computing
Technology changes fast. This chapter will introduce you to several areas that businesses will be trying to leverage in the coming years to gain an advantage over their competitors.
8.1 Artificial Intelligence
The field of Artificial Intelligence (AI) is composed of a wide range of subfields which are all concerned with understanding or building intelligent machines.

8.1.1 Knowledge Representation and Reasoning
An early application of AI in business was the use of expert systems. These systems have been used in a variety of businesses as well as fields like medicine, finance, and law.
Expert systems capture the “knowledge” of Subject Matter Experts (SMEs) within a database that can be efficiently navigated in order to answer questions and guide users toward more intelligent decisions.
8.1.2 Machine Learning
A machine is said to learn when it can improve its behavior through the study of past experiences and predictions about the future. A machine can learn in three ways:
- Supervised learning
The machine observes various examples of items that have been “labeled” in some way. For example, a program can observe various pictures of objects that have been correctly labeled with their names by human beings. This process of labeling data for a computer to learn from is very tedious and expensive.
- Unsupervised learning
Sophisticated learning algorithms allow machines to learn from data that has no labeling. With enough examples, the computer can create a “model” that can predict the identity of the object or what would come next in a sequence of objects. For example, language models can be constructed by feeding the computer enough text to be able to accurately predict the next word in the sequence.
- Reinforcement learning
This style of learning is somewhere between the first two. As the machine constructs a model, outside information is provided in the form of rewards or penalties in order to influence the model construction in the right direction. The rewards could be provided by humans or by the environment (e.g., a game that awards points). Not every piece of data needs to have a label or produce feedback, but the machine is not left in the dark either.
The inspiration for Artificial Neural Networks was provided by the biology of the human brain. Nodes are created within the model that represent neurons in the brain. Connections between the nodes (based on synapses between neurons) are either strengthened (when the information is present) or weakened (when information or confirmation is absent). In this way, the machine can “learn” which is the correct path for information to follow and/or which associations between nodes are more likely.
Deep learning involves a neural network model that is typically organized into many layers.
Large Language Models (LLMs) are deep neural networks that have been trained, using unsupervised learning, on very large datasets. These LLMs have proven to perform very well as the basis for the following kinds of systems:
- LLM-based applications: Search, summarization, and content generation engines.
- Chatbots: Conversational interfaces like ChatGPT.
- AI agents: Autonomous systems that plan and execute multi-step tasks like vacation planning.
Machine learning technology, like deep learning and large language models, has had a profound impact on businesses worldwide. Gartner predicts that AI spending will total $1.5 trillion in 2025 alone.
8.1.3 Natural Language Processing
Natural Language Processing (NLP) studies and creates machines that can communicate with humans and learn from what they have written.
NLP is used for a variety of purposes:
- Sentiment Analysis: Determining the emotional tone behind words.
- Named Entity Recognition (NER): Identifying and classifying key entities in text.
- Machine Translation: Automatically translating text from one language to another.
- Speech Recognition: Converting spoken language into text.
NLP has been an active field of study since the 1950’s. Today, LLMs are being used within NLP applications to enable more sophisticated and context-aware interactions with language.
8.1.4 Robotics
Robots have been used for repetitive and/or dangerous tasks for many decades (e.g., automobile assembly). The Tennessee Valley Authority (TVA) uses robots in situations where human lives or health could be at risk.

As technology advances, robots will be used in more areas of business and commerce. There are many areas, however, where robots have trouble. Fine motor skills that require a good sense of touch are difficult for robots and further research will be required to make progress.
8.1.5 AI Ethics and Privacy
AI ethics and privacy are crucial topics in the ongoing development and implementation of artificial intelligence technologies. The rapid advancements in AI raise important ethical considerations while also challenging our notions of privacy.
Core Concepts in AI Ethics
- Fairness:
- AI systems should be designed to make decisions that are fair and equitable, avoiding biases that could lead to discrimination against certain groups.
- Transparency:
- There is a need for AI models to be explainable, meaning users should understand how decisions are made. This transparency builds trust and accountability.
- Accountability:
- Developers and organizations should be held responsible for the actions of their AI systems. This includes addressing any harm caused by decisions made by AI.
- Beneficence:
- AI should be designed to benefit humanity and improve the quality of human life while minimizing undesired consequences.
Privacy Concerns in AI
- Data Collection:
- AI systems often require vast amounts of data, raising concerns over how this data is collected, stored, and used. Unauthorized data collection can infringe on personal privacy.
- Surveillance:
- The use of AI in surveillance technologies can lead to invasive monitoring, impacting civil liberties and privacy rights.
- Data Security:
- Ensuring the security of data used in AI is critical. Breaches can expose personal information, leading to identity theft and other consequences.
- Informed Consent:
- Users should be informed about data usage and have the ability to consent. Many AI applications lack clear consent mechanisms.
As AI continues to evolve, ongoing dialogue surrounding ethics and privacy will be essential for ensuring that technological advancements are aligned with societal values and respect for rights. This balance will define how AI impacts the future of privacy and ethics in our increasingly digital world.
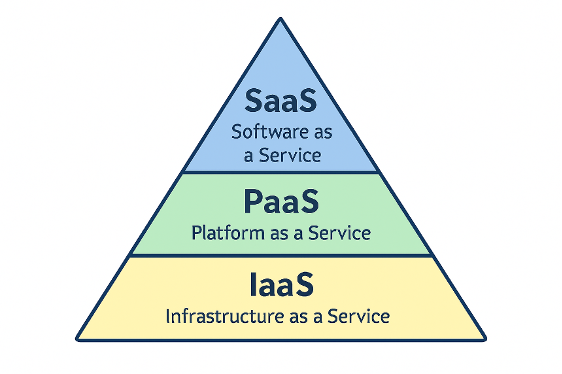
8.2 Cloud Computing
Cloud computing involves using computing resources (CPU cycles, memory, storage, software, etc.) that the customer does not necessarily control directly. These machines are usually housed in large data centers, operated by companies like Amazon, Microsoft, and Google.
These resources are made available as “services.” The most common kinds of services are:
- SaaS: Software as a Service – Gmail, Office 365, etc.
- PaaS: Platform as a Service – Windows environments (for example) that developers use to write and test code. The resulting code may be deployed as applications or services that are managed on the same or other platforms in the cloud.
- IaaS: Infrastructure as a Service – Hardware available to run the operating system of choice as well as application code or development tools.
In recent years these additional services have emerged:
- FaaS: Function as a Service – Small pieces of code that serve a single, granular function (e.g., process a payment).
- CaaS: Container as a Service – Isolated environments that can be built and executed on many different platforms (e.g., Docker containers that house and run websites or services).
Businesses are increasingly using these kinds of services instead of purchasing, operating and securing hardware that they must manage themselves.
8.3 Blockchain
The blockchain originated as the key technology behind Bitcoin, a peer-to-peer electronic cash system introduced to the world by its mysterious creator: Satoshi Nakamoto. A peer-to-peer network is composed of computers that all have the same level of authority. No single computer controls the behavior of any other.

The blockchain is a public ledger that records transactions. It is all but impossible to change transactions that have been recorded and since it is public, the blockchain ensures transparency and trust among users. The blockchain is also distributed among many computers which eliminates the need for a centralized authority or “clearing house.”
For example, if you use bitcoin to purchase a cup of coffee, that transaction is recorded on the blockchain for all to see. Furthermore, once it is recorded there is no way to change the date, the dollar amount or anything else that was recorded.
Miners analyze groups of transactions called “blocks” and tie each block in the chain to the previous block using advanced cryptographic algorithms. These miners can earn payments for their work (e.g., newly “minted” Bitcoin).
This public ledger technology is not only useful for cryptocurrency, but has also been used by many businesses that can benefit from a public ledger and the elimination of the need to “approve” transactions via a centralized authority. For example, Walmart uses blockchain to trace food products within their supply chain to quickly identify sources of contamination.
8.4 Quantum Computing
Quantum computers are fundamentally different than traditional computers. Traditional computers are based on binary digits (bits) that can hold either a value of zero or a value of one. Quantum computers use core principles based on quantum mechanics and quantum physics. Instead of bits that can have only one of two values, quantum bits (Qubits) can have multiple values that can change when they are measured. This strange behavior is not a mistake or error, but is rooted in the fact that the tiniest known particles have very strange behavior themselves.
Most quantum computers are very delicate. Even the slightest disturbance can destroy the quantum states (or values) of the Qubits. These computers require tightly controlled environments that keep the Qubits at temperatures at or near absolute zero (-459.67 degrees Fahrenheit).
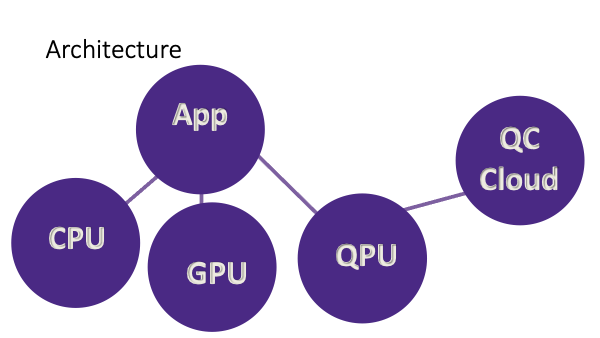
Classical computers will not be replaced by quantum computers. Quantum computers will be able to outperform traditional computers on some tasks, but not all. For these reasons, experts predict that our computers of the future will include a Quantum Processing Unit (QPU) similar to the Graphics Processing Unit (GPU) that gaming systems have today. The QPU may be able to perform some quantum-related tasks locally, but would delegate others to quantum machines that will be available as cloud services.
Quantum computers will be very helpful for researchers who are interested in studying chemistry and physics – especially at the micro level. They are also expected to have important applications in drug development, financial modeling, traffic optimization, climate research, and machine learning.
One application of quantum computing that has drawn the attention of the US Government, is quantum cryptography. Many algorithms and techniques that are widely used today to hide sensitive information will be vulnerable to quantum cryptographic attacks.
The National Institute of Standards and Technology (NIST) has identified several new algorithms that they have deemed to be quantum-safe – in other words, safe from future efforts to use quantum computers to reveal sensitive information.
Chapter Summary
Artificial intelligence is a very broad field that has a long history. Expert systems have been used in business for decades, but the new advances in Machine Learning and specifically in Deep Learning used to train Large Language Models have dramatically changed the way many companies have traditionally done business.
Robots also have a long history. Expect robotics to be used in new ways as research produces new breakthroughs. Cloud computing is used to provide many different levels of service today and will provide greater access to Quantum Computers in the future as quantum-based hardware matures.
The blockchain emerged as the basis for cryptocurrency systems, but has many other applications. As is the case with the other technologies in this chapter, you can expect businesses to find new applications for public ledgers based on blockchain in the near future.
Review Questions
8.1 What is Artificial Intelligence?
8.2 What are the three ways in which machines learn?
8.3 What are LLMs and what are they used for?
8.4 What are some of the ethical and privacy issues related to AI?
8.5 What are the five kinds of cloud services?
8.6 What is a blockchain and what does it do?
8.7 What will quantum computers be used for?
8.8 What does quantum computing have to do with the cloud?
Projects
8.1. AI According to AI: Ask AI to explain itself. What is it? How does it work? Where did it come from?
8.2. AI Ethics: Ask AI what are some important ethical and privacy considerations and what does it suggest we do to address those issues? Do you agree with the suggestions?
8.3 Personal Cloud Information: List all of your personal and/or private information that is currently stored in the cloud. What would happen if you no longer had access to the internet? Would the loss of those items concern you? What if your data was made available to everyone?
8.4 Blockchain Viewer: Search for a “blockchain viewer” with any browser’s search engine. What information is visible to you? Is there any information that you wonder about or might be missing?
Credits:
Portions of chapter 8 were contributed and/or improved by Duck.ai
https://cdn.pixabay.com/photo/2024/12/07/08/47/artificial-9250465_640.jpg
https://pixabay.com/illustrations/digital-artificial-technology-brain-9301910
https://pixabay.com/illustrations/bitcoin-cryptocurrency-crypto-3089728
